The Smart Factory Requires Security

The new web view for production data is online. Employees can now access live data anywhere and anytime from their smartphones. But how do they know that only authorized employees have access to current production figures and to data in the cloud? Smart Factories and IIoT require expert knowledge to ensure software is as secure as possible and to prevent unauthorized access.
- Secure operation for IIoT and the Smart Factory
- User authentication and authorization for access security
- Make security updates and upgrades while production is underway
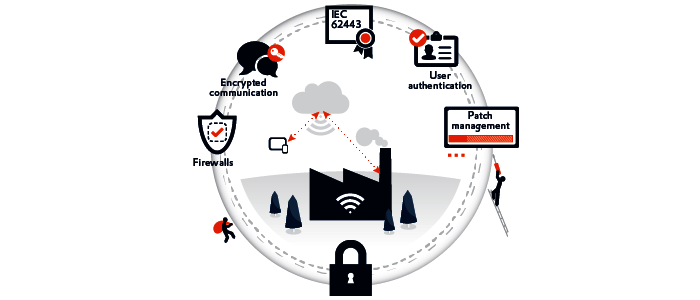
zenon provides you with crucial technologies to protect your production sites from cyber attacks. Key components of these technologies include integrated user administration and authentication, robust encryption mechanisms, and much more.
Only up-to-date systems are secure systems
Production plants used to be pretty much isolated from the outside world. Yet IIoT and Industry 4.0 require a wide range of connections and ports for external access. As a result, the topic of cyber security is becoming more and more important for production plants. Cyber attacks are becoming increasingly real risks. And gaps in security need to be detected and closed. But when doing this, the specific conditions of production plants also have to be observed. For example, installing a security patch must not lead to production being stopped. The argument that you should “never change a running system” and put off updates for as long as possible if production is running smoothly now represents a major risk factor. Gaps in security need to be closed early on to ensure that the company's regulations are always up to date.
How zenon supports your security precautions
For many versions, it has been possible to update zenon while production is under way without the need for downtime. This makes it easy for you to continually benefit from up-to-date security standards and new features.
When it comes to user authentication too, zenon is on your side. In addition to zenon user administration, Active Directory is also supported. Logins and access rights can then be conveniently linked to Windows user authentication. Easy-to-configure authorization levels ensure that only users authorized to do so can perform an action. It goes without saying that the entire communication chain is highly encrypted, provided the connected machines support this. You are, therefore, not only safeguarding communication within the company, but also safeguarding access via mobile communication.











































